Yes, you and your staff are the biggest risk to your business. This is an actual case study of a cyber-crime that we dealt with in 2018.
Yes, you and your staff are the biggest risk to your business. This is an actual case study of a cyber-crime that we dealt with in 2018.
The Start
A local company in Yorkshire (previously unknown to us) approached us, asking us to come and take a look at one of their computers, they had been hacked.
On investigating it was apparent that they hadn’t just been hacked; in-fact they had lost a six-figure sum. It was an existential threat to their business.
We have standard protocols for dealing with cyber attacks, and in this case we immediately:
- Quarantined the computer in question
- Conducted a full security sweep of their systems followed by password changes
Day One actions
During this first contact, we observed signs of bad practice. A USB stick was lying next to the infected computer.
‘What’s that doing there?’ I asked.
It turned out that they had been advised to take a copy of software and data they needed from the infected PC and transfer it to another PC on their network so they could continue working on the data in question. (Astonishingly, they had been advised to do this by their principal software provider!). This meant there was a risk that malware had also been transferred.
We quarantined another PC and then the whole network, followed by a full security sweep.
Follow-on actions
Having plugged the immediate gap, we were asked to conduct a complete examination to confirm what happened, how it happened and to report on the same.
We were also asked for recommendations on their wider cyber security arrangements.
Our findings were quite illuminating.
What the hackers did
A Phishing email was sent to one of the client’s generic email accounts. One person monitors these and this one, marked for the attention of accounts, was forwarded on to the accounts team.
Only one person was in the accounts department that day. They opened the email and downloaded the attachment. Nothing happened, so they disregarded it and moved on.
That night the hackers were in and out in under an hour. The attachment had opened a direct link from the hackers to the individual PC. They accessed the client’s accounting system and changed the bank account details of their eight largest suppliers. They then logged out and did nothing else, so there was no sign that anything untoward had happened.
Until 6 weeks later when suppliers started to ring up and ask where their monthly payments were. That’s when we were called in.
What we did
We produced a police-actionable report on our findings and this was submitted to local police and cybercrime units in London. The hackers appeared to be in Hungary, but in fact, were traced to South-East England.
The perpetrators were found and successfully prosecuted in September 2018. All but £9k of the stolen funds were recovered. Obviously, the client was relieved and delighted with this given the circumstances.
However, it could, and should have been zero, and here are the reasons why.
How it could have been prevented – the biggest risk to your business
The client did not have professional IT management in place – they thought (incorrectly) that their software provider took care of it. Had professional IT support been in place, the software that infected the original PC would not have done so – no download would have been allowed through automated procedures. Even if the software had somehow got through, the hackers would not have been able to gain access to the accounting systems, again due to procedures and policies that professional IT management would establish.
None of the staff had cyber hygiene training. With that training, either (or both) of the email recipients could have spotted the potential issue.
Protective monitoring software would have spotted the incoming email and also the late-night access. No such software was in place.
So, there was any number of ways that the attack could have been foiled. As the title states, you and your staff represent the biggest risk to your business succumbing to online crime.
Cybercriminals depend on two things:
- Trust – or to put it another way, a lack of cyber hygiene knowledge. The human factor is responsible for 80% of successful cyber crimes
- Poor IT setup and systems– it’s a false economy to set up and manage your own IT systems if you aren’t a trained IT professional
Summary
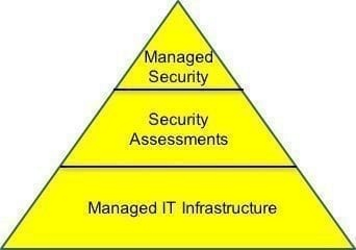
Since this event, the client has implemented professional IT support (through us), cyber security software (from us) and IT policies in accordance with our recommendations.
A fascinating story right?! Before you close this webpage, let me ask you -are you going to act right now on your cyber security arrangements?
Yes? Good. You should. You can start by requesting our free cyber assessment questionnaire, or arranging an online call with us to conduct it with you face-to-face. We’ll assess your cyber risk and send you our recommendations, free of charge, no catch.
Later? When? Why the delay? Cybercrime is the fastest growing criminal enterprise in the world, it is the biggest risk to your business.
No? OK, well thanks for reading and best of luck! Remember – the biggest risk to your business succumbing to online crime is you and your staff.
We don’t ever want to say ‘told you so’…