Author: Guy Phoenix
Is Microsoft Copilot Safe for Your Data?
Looking For IT Support in Yorkshire?
Antivirus vs Managed EDR: Which Is Better For Your Leeds Business?
7 Mistakes You’re Making with Your Windows 11 Rollout (and How to Fix Them)
7 Mistakes You’re Making with MFA and Cloud Security (and How to Fix Them)
7 Mistakes You’re Making with Cyber Essentials
How to Choose the Best IT Support in Leeds (Compared)
If you run a business in Leeds, you already know that this city moves fast.
The Top 5 Phishing Techniques Targeting Staff This Year
What Fails Most Cyber Essentials Assessments — and How to Avoid It
What Fails Most Cyber Essentials Assessments — and How to Avoid It
Preparing for Cyber Essentials certification is one of the most effective ways to strengthen your organisation’s cybersecurity posture, but many businesses still fail to address avoidable issues. Recent assessment insights show that most failures stem from gaps in basic cyber hygiene rather than advanced threats.
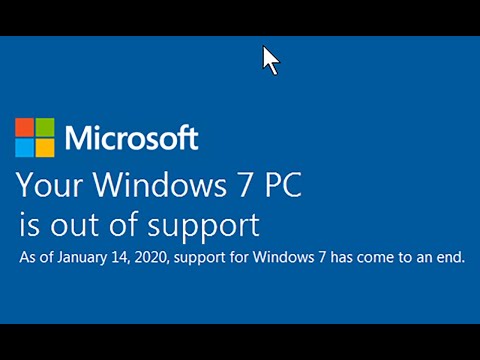
The most common reason organisations fail is outdated or unsupported software. Assessors frequently discover end‑of‑life operating systems, unpatched routers, old browsers, and mobile devices that haven’t received security updates within the required 14‑day window. Even a single unsupported device can result in automatic failure because Cyber Essentials requires all critical updates to be applied promptly. Many teams simply aren’t aware that some systems are out of support, underscoring the importance of strong asset management and consistent cyber awareness.
Another major source of failure is misconfiguration and weak internal processes. Organisations often believe they are compliant, but vulnerability scans expose hidden issues, missing documentation, and poor evidence of patching or MFA enforcement. These gaps remain some of the most frequently cited pitfalls in audits.
From April 2026, Multi‑Factor Authentication (MFA) becomes even more critical. Where a cloud service offers MFA, and it is not enabled, the assessment will automatically fail—no exceptions. This reflects MFA’s role in preventing credential‑based attacks, especially as AI‑driven cyber threats escalate.
How to Avoid These Common Failures
- Keep a complete and current asset inventory
- Apply critical patches within 14 days
- Enable MFA on all cloud services
- Strengthen organisation‑wide cyber awareness
- Conduct pre‑assessment scans to identify misconfigurations early
How Fresh Mango Technologies Can Help
As qualified Cyber Essentials Assessors, Fresh Mango Technologies can guide you through every step of the certification process—from readiness checks to remediation support—ensuring you meet the latest requirements with confidence.
Why Cyber Essentials Still Matters in an AI-Driven World
As AI tools become embedded in everyday business operations, many organisations assume that newer technology automatically delivers stronger security without the rigorous processes of Cyber Essentials accreditation. In reality, most successful cyber attacks still exploit basic, preventable weaknesses — not advanced AI systems.
Issues such as weak passwords, unpatched software, poor access controls, and low staff cyber awareness remain the most common entry points for attackers. That’s why Cyber Essentials accreditation continues to play a critical role in modern cyber risk reduction.
Cyber Essentials is a UK government-backed cybersecurity framework designed to help organisations defend against the majority of common cyber threats. It focuses on practical, high-impact controls including secure configuration, device protection, access management, malware defence, and update management. These foundations are even more important when businesses adopt AI platforms and cloud services, which expand the attack surface.
Achieving Cyber Essentials certification is not just a compliance exercise — it is a business resilience strategy. It demonstrates security maturity to customers, partners, and insurers while reducing the likelihood of costly incidents.
Fresh Mango Technologies supports organisations through Cyber Essentials certification, cyber awareness training, and AI risk governance. The goal is not only to meet standards, but to build confident, secure ways of working with both traditional IT and emerging AI tools.
Strong security fundamentals still stop most attacks — even in an AI-driven world.
The Hidden Cost of Convenience: AI, Data Privacy, and Business Risk
Generative AI tools such as ChatGPT, Claude, and Google Gemini are now part of everyday business life and make AI Data Privacy a real concern. They help teams work faster, generate ideas, and reduce manual effort. Used well, they can be a real competitive advantage.
However, like any powerful technology, AI comes with risks — particularly around data privacy, security, and compliance. These risks are often overlooked in the rush to adopt new tools.
What Really Happens to Data Entered into AI Tools
Most public AI platforms improve their performance by learning from user interactions. This means that information entered into prompts may be stored and reused as part of ongoing model development.
If employees paste in sensitive material — such as client contracts, internal reports, pricing models, or proprietary ideas — that data may no longer be fully under your organisation’s control. While this doesn’t mean the information will be openly shared, it does introduce a real risk of unintended data exposure.
Why This Matters for Businesses
For organisations, this goes beyond general privacy concerns. Uploading personal or sensitive information into public AI tools can create regulatory and legal exposure, particularly under data protection laws such as:
Once data has been absorbed into an AI model, it cannot realistically be removed. This makes post-incident remediation extremely difficult and undermines obligations such as the “right to be forgotten”.
The Rise of Shadow AI
A growing challenge for many businesses is Shadow AI — the use of AI tools by employees without formal approval, guidance, or oversight from IT or security teams.
Without clear policies or enterprise safeguards, sensitive company information may be uploaded to third-party platforms with unclear data handling practices. This can expose intellectual property, commercial strategy, and customer data to unnecessary risk.
Using AI Safely and Effectively
At Fresh Mango Technologies, our advice is straightforward:
Never treat public AI tools as secure data environments.
Best practice includes:
-
Anonymising information before analysis
-
Avoiding the use of personal data, client details, or confidential material
-
Educating teams on what is — and is not — appropriate to share
For organisations that want to use AI at scale, enterprise-grade AI solutions offer a safer path forward. These typically include data isolation, strong security controls, and contractual assurances that business data will not be retained or used for training.
AI Is a Tool — Governance Makes It an Asset
AI has enormous potential to improve productivity and decision-making. But without proper controls, it can quietly introduce risk into the heart of your organisation.
In today’s digital economy, data is one of your most valuable business assets. Protecting it isn’t about slowing innovation — it’s about enabling AI adoption in a way that is secure, compliant, and sustainable.
Used responsibly, AI becomes a powerful partner. Used carelessly, it becomes an invisible liability.
How Cyber Essentials is having a demonstrable positive impact
Cyber Essentials positive impact
The evidence is now clear and unequivocal – Businesses that adopt Cyber Essentials experience a huge reduction in cyber incidents.
IASME (Information Assurance for Small and Medium Enterprises), who oversee the CE scheme, has been gathering data from insurance companies. The results are eye-opening.
Insurance data indicates that certified organisations are 92% less likely to make a cyber insurance claim than those without the certification. Additionally, implementing the scheme’s core controls can prevent around 80% of common cyber attacks, according to IT Governance Ltd. Here’s a more detailed breakdown:
Reduced Cyber Insurance Claims
The Cyber Essentials certification is associated with a substantial decrease in the likelihood of needing to file a cyber insurance claim.
Prevention of Common Attacks
The scheme’s technical controls are designed to stop the vast majority of basic, “commodity” cyber attacks.
Third-Party Risk Management
Cyber Essentials is also used as a tool to manage risks within supply chains, leading to fewer cyber incidents overall.
Specific Case Study
The financial services company, St. James’s Place, saw an 80% reduction in cyber incidents after requiring its partners to become Cyber Essentials Plus certified, according to IASME.
So, the data and evidence are compelling. If you would like to get started on your Cyber Essentials journey, contact Fresh Mango today.
Why do people fall for cyber scams?
Why Do People Fall for Cyber Scams?
In today’s digital age, cyber scams are more sophisticated than ever, yet people continue to fall victim to them. But why? The reasons are more complex than mere gullibility—they stem from psychology, social engineering, and even human nature.
The Psychology of Deception
Scammers understand human psychology better than most. They exploit emotions like fear, urgency, and greed. An email warning that your bank account has been compromised triggers panic, leading you to act before thinking. Similarly, an offer promising quick riches plays on greed, clouding judgment.
Social Engineering Tactics
Cybercriminals use social engineering — manipulating people into revealing confidential information. They impersonate trusted entities like banks, government agencies, or even colleagues, making their requests appear legitimate. When faced with an urgent message from “the boss” demanding sensitive information, people may comply without second-guessing.
Lack of Cyber Awareness
Despite increased awareness campaigns, many people still lack a solid understanding of online security. Weak passwords, clicking on suspicious links, or failing to verify sender authenticity—these mistakes expose them to cyber risks. Scammers rely on ignorance, creating convincing schemes that seem entirely plausible.
Technology Making Cyber Scams More Convincing
Advancements in AI and deepfake technology make scams harder to detect. Phishing emails look more authentic, fraudulent websites appear legitimate, and voice scams can mimic real people. As cyber criminals refine their techniques, distinguishing between genuine and fraudulent messages becomes increasingly difficult.
How to Avoid Cyber Scams
While scams are constantly evolving, vigilance remains key. Always verify sources, question unexpected requests, and stay informed about the latest cyber threats. Cyber awareness isn’t just for IT experts—it’s essential for everyone navigating the digital world.
Have you ever encountered a cyber scam? What made it convincing?
The Importance of Anti-Spam Software in Cybersecurity
The Importance of Anti-Spam Software in Cybersecurity
In today’s digital age, email remains a primary communication tool for both personal and professional use. However, this widespread usage also makes it a prime target for cybercriminals. Spam emails, which are unsolicited and often malicious, can flood inboxes, leading to potential security risks. As a cybersecurity analyst, it’s crucial to understand the role of anti-spam software in protecting against these threats.
What is Anti-Spam Software?
The software is designed to prevent potentially harmful emails before they reach the user’s inbox. These tools use a combination of techniques, including content filtering, blacklisting, and machine learning algorithms, to identify and filter out spam.
Key Features of Anti-Spam Software
- Content Filtering: This involves analyzing the content of emails for common spam indicators such as suspicious links, excessive use of certain keywords, and unusual formatting. Content filtering helps in identifying and blocking spam based on the email’s content.
- Blacklisting: The software maintains a list of known spam sources. Emails from these sources are automatically blocked. This list is continuously updated to include new spam sources as they are identified.
- Machine Learning: Modern tools leverage machine learning algorithms to improve their detection capabilities. These algorithms analyze patterns in email data to identify new types of spam and adapt to evolving threats.
Benefits of Using Anti-Spam Software
- Enhanced Security: By blocking spam emails,the software reduces the risk of phishing attacks, malware infections, and other cyber threats.
- Improved Productivity: With fewer spam emails to deal with, users can focus on legitimate communications, leading to increased productivity.
- Cost Savings: Reducing the risk of cyber attacks can save organizations significant amounts in potential damages and recovery costs.
In conclusion, anti-spam software is a vital component of a comprehensive cybersecurity strategy. Effectively filtering out unwanted and harmful emails helps protect users and organizations from a wide range of cyber threats. As cyber threats continue to evolve, the importance of robust anti-spam measures cannot be overstated.
Computer Studies ‘O’ Levels in Abu Dhabi
How a Microsoft Phone Scam nearly destroyed a business
Why Cyber Essentials has a positive impact for SMEs
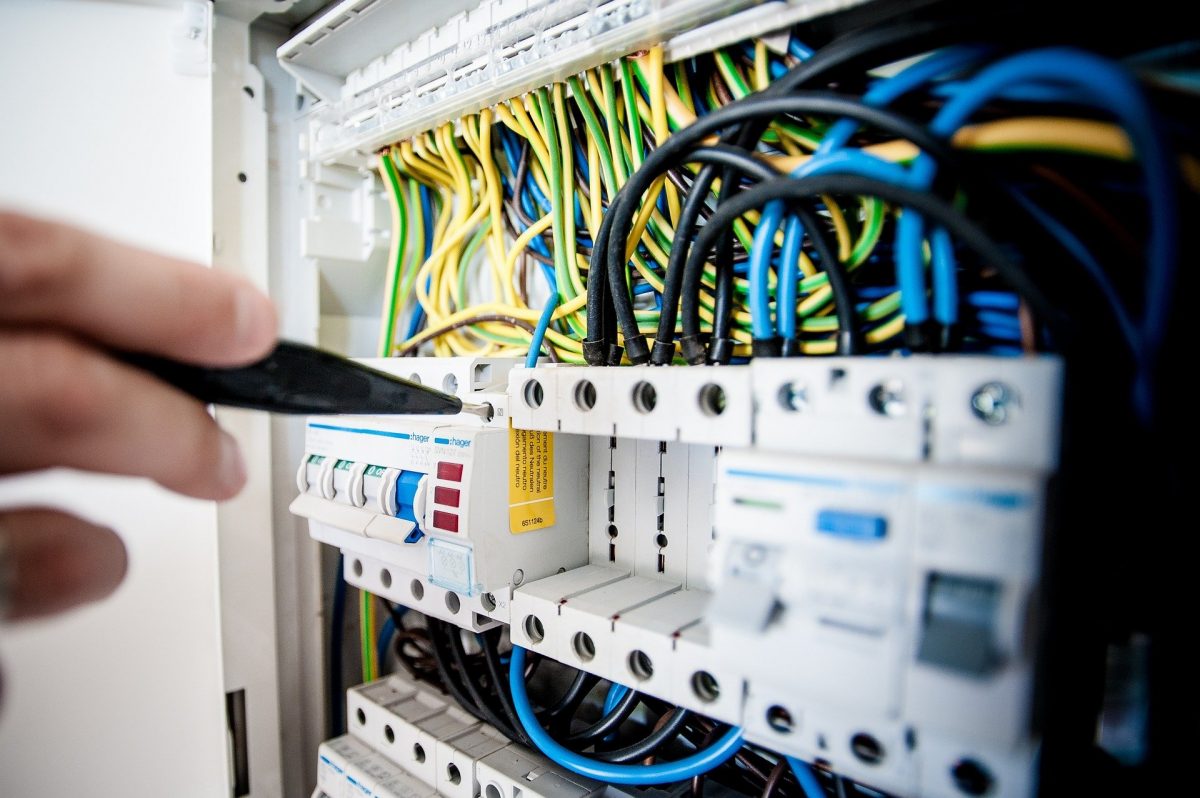
How professional IT Support improves your cyber security
My first home computer
Atari Game Console
How long have you been in IT?
I’m often asked if I’ve been in IT all my life. In terms of career roles, the answer is ‘no’ since I’ve been fortunate to hold a variety of positions in the companies I’ve worked for and owned.
But I thought about the question a bit more recently and realised that I’ve had an interest in electronics/IT/computers for as long as I can remember. I can still remember the surprise (or was it exasperation?!) on my parent’s faces when they asked me what I would like for my birthday, and I told them I would like one of the new electronic calculators that had just come out.
I was 7 years old!
I’ve turned the house upside down but can’t find that original calculator. I was able to unearth a picture of one like it and attach it here. It’s interesting to see that calculators haven’t actually changed that much, so it was amazingly ahead of its time.
So there you have it, my new answer to the question of ‘how long have you been in IT’ will be ‘as long as I can remember’!
Guy Phoenix is the Managing Director of Fresh Mango Technologies and Their sister company in the British Virgin Islands.
Going to the Dentist
The importance of cyber awareness aka cyber hygiene
Top Three Cyber Security Tips
Did you forget your Microsoft 365 password?
How Professional IT Support saves money
I’m CEO, I should have Admin credentials!
Why engage an IT company rather than a ‘one-man-band’?
Do I have to upgrade to Windows 11 yet?
IT Whack-a-mole
DO YOU FEEL LIKE YOU’RE PLAYING IT WHACK-A-MOLE? ONE PROBLEM GOES AWAY, AND ANOTHER ONE APPEARS? WORSE, THE SAME ONE COMES BACK?
Do you feel like you’re playing IT whack-a-mole? One problem goes away, and another one appears? Worse, the same one comes back?
Proactive IT support from Fresh Mango Technologies is designed to stop the problem from occurring in the first place! And when you do get a problem, we fix it AND the cause. So you won’t have to ‘whack’ it again!
Stop playing whack-a-mole with your IT support with proactive IT support from Fresh Mango Technologies UK.
You’re not alone. ‘IT Whack-A-Mole’ issues affect the entire IT world. Many modern professionals in IT use the term ‘IT Whack-a-mole’ to refer to processes or pervasive problems that just keep occurring, even after you think you’ve fixed them.
These types of problems are common in a lot of businesses, with hardware & software that fails routinely such as printers, monitors or email. These sorts of issues have become so commonplace in many places they’re the expected norm. We want to change that.
We understand that these are critical tools you need to get your job done and losing them, again and again, sets your business back exponentially. Failure in even one of these areas can bring work to a halt for many businesses, costing you time, resources and money.
We believe the route of these issues lies in poor IT support from companies or individuals who lack the expertise and knowledge to offer truly proactive IT support. Support from Fresh Mango Technologies UK, however, is different. Our team is reliable, dependable, experienced and professional, offering a unique approach to support.
Our approach to IT support means our technicians not only resolve the issues at hand but go above and beyond to ensure the stability of your system even after we’ve stopped working on it. We answer why and how a problem occurred and better yet, provide you with professional experienced advice on how your systems can be improved and adapted to never experience this issue again.
With over 30 years of successfully providing computer, website and IT support across the UK and Caribbean, you know you’re in safe hands. We pride ourselves on rapid response and our friendly, professional, highly qualified engineers who are trained to understand your needs and deliver sound advice and the right solution the first time.
You may also be interested to read our blog piece on the ideal IT System setup.
If you enjoyed this article you may also be interested in Children & Technology: Cookies, Webs & Touchscreen.
Microsoft Out of support dates
When you hear ‘Microsoft Out of Support’ mentioned it may not be clear what that actually means. We’ll explain it below, as well as advise on some of the key dates relevant to Microsoft Products.
A Day in the Life of an IT Support Technician
I thought it may be interesting to write up what a typical day as an IT Support Technician at Fresh Mango Technologies is like.
I thought it may be interesting to write up what a typical day in my life as an IT Support Technician at Fresh Mango Technologies is like. So I worked with one of our team members on a random day (a Tuesday last month) and kept a diary of everything he did that day.
It turned out to be a lot of fun and I hope you enjoy reading it as much as I did writing it!
IT Support Technician – a ‘typical’ day
Well let’s put something to rest immediately – there’s no such thing as a typical day for an IT Support Technician! We certainly plan the weekly work for the team, and so on a day-to-day basis, they always have a clear schedule in place. However, we never know when a customer may have an urgent IT matter that requires a ‘DER’ (Drop-everything request) and so all plans are fixed in stone until they aren’t!
Fortunately, we don’t get many DERs – with continuous monitoring of customer systems and regular ‘patching’ and other health checks – we keep problems to a minimum. That doesn’t mean they don’t occur though, as we were to see on this particular Tuesday… Here’s how it played out. It’s written in the first person from our technician’s perspective.
Leaving Home
I left home at 730AM to ensure I could beat the traffic and be at our customer premises near Leeds for an 8 AM scheduled onsite visit. The relatively early start was to ensure minimal disruption to the customer (their staff mostly start at 9 AM). This particular customer has quarterly visits and their systems are relatively new, so I anticipated a pretty smooth visit.
After checking in I went to the server room to conduct physical checks and updates of systems. This took around an hour, and then I did a ‘touch check’ of every PC and laptop available. This entails simply talking to every member of staff and asking if they have any IT issues. We find that sometimes people will suffer an annoying issue and they don’t raise it as a support request. By ‘touch checking’ everyone we can iron out any niggles whilst on-site and it’s always appreciated.
At the same time, I handed out special offer cards, ensuring each PC is labelled and had ‘How to contact us’ stickers on them. I found a couple missing and added them.
10 O’Clock
Back to the Leeds office and to my desk to conduct scheduled work and to help deal with any tickets (support requests). It was a busy day. Microsoft had issued an ‘Emergency patch’ update overnight. This means that Microsoft has found a security issue with their operating software, and so the software needed to be updated on all customer computers as soon as possible. So I set about scheduling overnight updates for the customers that had been assigned to me.
Lunchtime (1230)
Having gotten through all my updates, I headed for some lunch. I usually bring something into the office, but I had another scheduled on-site visit with a customer south of Leeds so decided to eat ‘on the hoof’. This was for a straightforward installation of 2 new PCs.
I arrived at the customer premises at around 1 PM and installed the computers. I asked the users to ensure they were set up to their liking (they were) and also did a quick check of their server (not scheduled but I think it’s good practice). Just as I was getting ready to head back to the office, I received a call from Bruno (our Technical Manager). He wanted me to head straight to another customer just a couple of miles away. They had just called to say they thought they may have been hacked. OK, foot-down time!
245 PM
Arrived at the customer’s premises. Bruno had briefed me en route and one of our senior technicians was also accessing their systems remotely to run security checks. Strictly speaking, we didn’t necessarily need someone on-site, but when a customer thinks they have been hacked we always establish an on-site presence as quickly as possible. This is in case we need to isolate a device, or the entire network if a sustained cyber attack is underway.
Fortunately, that was not the case with this particular event. We quickly found the source of the hack – a single PC – and so I immediately quarantined it. This is of course disruptive for the individual using it, but we can’t risk a hacker gaining access to other systems, nor do we wish to see ransomware spread across their network. Having confirmed with Bruno that all scans were negative, I headed back to the office with the quarantined computer so we could diagnose what happened and clean it of any malware.
4 PM
Arrived back at the office, and with assistance from Bruno, we began the diagnosis. As is so often the case, we found that the user had clicked on a ‘phishing’ email. This particular link took the user to a convincing, but fake, Microsoft login screen. This in turn asked for credentials that they had entered. So, the first thing to do was to reset their password, which I did. We then ran a full security sweep of the PC and confirmed no other ‘nasties’ were on it.
That was a close shave for the customer – fortunately the individual who had clicked on the link had the presence of mind to realise something may have been untoward and had notified us accordingly.
545 PM
Time to head home. I arranged for another member of the team to return the quarantined PC to the customer first thing tomorrow since my schedule was taking me to see three clients in North Yorkshire.
So there you have it – a typical day for an IT Support Technician. And it’s still only Tuesday…!
Computer tax relief
The Chancellor recently announced an extension to the super-deduction corporation tax relief measure, effectively providing computer tax relief.
Computer tax relief – New temporary tax reliefs on qualifying capital asset investments from 1 April 2021
The Chancellor recently announced an extension to the super-deduction corporation tax relief measure, effectively providing computer tax relief.
This means when you purchase (not lease) qualifying investments you can claim 130% tax relief on them until 1st April 2023. This means you should be able to obtain computer tax relief on any computer systems you purchase until that date.
Of course, you should check the position with your accountant before claiming computer tax relief.
So, don’t delay, now’s a great time to commence your computer system upgrades!
You can read the full report from HMRC here.
What you should consider for your IT systems
First and foremost you should review your computer server and determine if it is time to upgrade. If you are still operating on Windows server 2012 then you really have no choice, since this will soon be out of support by Microsoft. Notwithstanding that, if your server is (or will be) 5 or more years old, it’s really time to consider a new one.
Associated with servers is network equipment. Lead times for this equipment, notably switches, are hugely problematic. You should plan on a 6-month lead-time. That means you should start planning now if you wish to have your new IT system in place before the April 2023 deadline.
Finally, you should consider upgrading all your PCs and Laptops. If they are still operating on Windows 10, keep in mind that Microsoft will end support for Windows 10 in 2025. At that point you will need to upgrade to Windows 11. Note that in order to run Windows 11, PCs require a minimum hardware specification. So it is worth considering making the change to Windows 11 now.
Excerpts from the report
General description of the measure
This measure will temporarily introduce increased relief for expenditure on plant and machinery. For qualifying expenditures incurred from 1 April 2021 up to and including 31 March 2023, companies can claim in the period of investment:
- a super-deduction providing allowances of 130% on most new plant and machinery investments that ordinarily qualify for 18% primary rate writing down allowances
- a first-year allowance of 50% on most new plant and machinery investments that ordinarily qualify for 6% special rate writing down allowances
Policy objective
This measure is designed to stimulate business investment. It does so by increasing the incentive to invest in plant and machinery by offering higher rates of relief than were previously available.
Add extra security to your systems with TFA
In this blog piece, I’ll discuss how to add extra security to your systems with two-factor authentication (TFA). It’s actually very straightforward and provides a step-change improvement to your security.
In this blog piece, I’ll discuss how to add extra security to your systems with two-factor authentication (TFA). It’s actually very straightforward and provides a step-change improvement to your security.
What is Two-factor Authentication?
Two-factor authentication protects your applications by using a second source of validation, like a phone or token, to verify user identity before granting access. It is engineered to provide a simple, streamlined login experience for every user and application, and as a cloud-based solution, it integrates easily with your existing technology.
Add extra security to your systems – Our recommended TFA solution
We have tested several solutions for TFA/MFA and have chosen ‘Duo’ as our preferred offering. Duo is fast and easy for users to set up, and with several available authentication methods, they can choose the one that best fits their workflow. No headaches, no interruptions — it just works.
Because Duo functions like a gateway for your existing and future IT infrastructure, it’s the perfect solution for growing businesses of any size. Set up new users and support new devices at any time, and protect new applications almost instantly — without impacting legacy technology.
Duo natively integrates to secure any application or platform, so whether you’re adding 2FA to meet compliance goals or building a full zero trust framework, Duo is the perfect addition to your security portfolio.
- Multi-cloud, hybrid, or on-premises environments
- SAAS tools, critical infrastructure, custom applications, and even SSH
- Secure remote access
Add extra security to your systems – An example deployment
We use a bespoke management system called JIM. We continuously maintain and improve the security of the system. We implemented Duo so that, even in the unlikely event that a hacker cracks one of our encrypted passwords, they would still not gain access. The account owner would receive a TFA push request on their smartphone, and be immediately alerted to the attempted unauthorised access. So a double-win! Hacker prevented from access, user alerted to attempted hack.
Get Started with TFA!
So why not get started and add extra security to your systems with TFA? It’s straightforward to set up and for your team to use. What’s more, you’ll sleep that little bit easier knowing you have significantly improved your online security.
Current Supply Chain and Cyber challenges
Wow, nearly May already! Another month chalked off 2022, the year is whizzing by again… This month we have two updates from the world of IT that are impacting everyone.
FRESH MANGO TECHNOLOGIES TESTIMONIAL
Allott and Associates Ltd’s relationship with Fresh Mango (originally CCS 2000) has flourished since they came to our rescue when we had server issues caused by a hard disc problem…
Allott and Associates Ltd’s relationship with Fresh Mango (originally CCS 2000) has flourished since they came to our rescue when we had server issues caused by a hard disc problem. This involved working to a critical deadline – which our original supplier based in Wales was unable to meet.
At short notice Fresh Mango was able to resolve the issue, installing new mirror drives. Since then, the companies’ relationship has gone from strength to strength. Fresh Mango now supplies Allotts with computers, supports our entire network and successfully deals with any technical challenges ranging from system failures to resolving encryption issues to ensure our UK GDPR compliance.
Overall, we are delighted with the service provided by Fresh Mango and recently renewed our contract for a further 12 months. Keep up the good work!
Testimonial – Philip Allott – Allott and Associates Ltd
What is the ideal setup for my IT systems?
In this blog, I will set out the ideal setup for your business IT systems. It represents current best practices for small and medium-sized businesses, with an…
Good question! Take a look at our blog piece (s) on the subject:
The Ideal setup for your IT Systems (Part 1)
In this blog, I will set out the ideal setup for your business IT systems. It represents current best practices for small and medium-sized businesses, with an…
Why do Hackers Hack?
Interesting question! We’ve written a blog piece on this subject of hackers, you can read it here: https://freshmango.co.uk/blog/why-hackers-hack/
Long story short – don’t take it personally if you get hit – it’s usually not you that they are targeting, even though it feels very personal.
You may also enjoy this blog piece.
Why Hackers Hack
Victims of hacks and attempted hacks often take it personally. Why did they come after me? I’m not famous or rich. Why did they come after my company? We’re just a small business…
Why do Hackers Hack?
Victims of hacks and attempted hacks often take it personally. Why did they come after me? I’m not famous or rich. Why did they come after my company? We’re just a small business.
That’s a perfectly natural human reaction. The fact is that cyber-attacks are rarely personal or business-specific.
Hackers are ready to exploit any security crack without taking into consideration who you are or what you do. Here are some of the things that motivate them:
Money
Cyber-attacks do not often result in immediate monetary gain. Hacks allow cybercriminals to extract information that can be exploited for financial gain. For example:
- Credit card information
- Contact information to be sold to unethical marketing lists.
- Username and password logins, to access and take over server resources, and to attempt dictionary attacks.
- Sensitive or proprietary information to sell or extort.
- High-security information to compromise the premises of a facility
Resources
You might think that your business is not big enough for someone to be interested in tapping into your traffic or your authority. However, cybercriminals will often attack an entire web server. As a result, your small website might just end up being a part of a big hack.
Cudos
Some hackers break into targets just to prove they can. They also show off their craft by forcing access and stealing valuable information.
Social Justice
Hackers may pursue a religious or political agenda and use their skills to deface targets.
So if (when…) it happens to you, try not to take it too personally…
Why don’t I have Administrator Credentials on my PC or Laptop?
Why don’t I have Administrator Credentials?! We’re asked this question from time-to-time, and the short answer is it is standard IT policy for any professionally managed IT network…
Why don’t I have Administrator Credentials?! We’re asked this question from time-to-time, and the short answer is it is standard IT policy for any professionally managed IT network. If you’re keen to understand why this is the case then read on!
IT History – Standardisation
In any business or organisation, standardisation in your IT systems is an essential factor in ensuring smooth and efficient operation. Imagine a situation where every single device was set up in a bespoke manner. No standardisation, differing password policies, differing software, differing access rights to directories and so on. Every user of any device able to make amendments to their PC/laptop as they see fit.
Now try to imagine administering and managing such an IT system from an IT Management perspective. Any time a staff member had a problem, the IT technician would have to run a huge amount of diagnostics in order to figure out what may be going wrong. This is because each PC/laptop has a non-standard setup and settings may have been changed by the user since the last time the computer had an issue.
It shouldn’t be too difficult to realise that managing such a chaotic approach would make the IT management nigh-on impossible. This would lead to significant knock-on effects, not the least of which would be dramatically reduced inefficiencies in the workforce.
So, in keeping with any operation, standardisation is the watchword for efficiency. IT is no different.
That’s the backdrop for why standard IT policies are so important. To the specific issue raised in the blog-title, standard users don’t have the ability to change settings on their system or download software. The former is part of IT standardisation, the latter relates to cybersecurity, which I will come onto next.
Why do you need Administrator credentials?
If a user is insisting on Administrator credentials, the question you need to ask is ‘why do they need them?’ Most people leave car maintenance to the experts. In these days of electronic engine management, it takes an expert to conduct a full car service or repair.
In other words, just because you can drive the car, you don’t mess with what’s under the bonnet (the hood for our US readers). Just because you know how to use your PC/laptop – why do you want or need the ability to mess with ‘what’s under the bonnet’?
Administrator credentials are best left in the hands of professionals who, to be blunt, know what they are doing.
The Cybersecurity problem
Let’s say you, the user of your computer, have Administrator credentials. Let’s also say you don’t go near the operating system or settings. What you do, however, is download software. It may be perfectly legitimate software. So what’s the problem?
Imagine you click on a link in an email. The email looked legitimate. Nothing happened when you clicked the link. No foul no harm, right?
Wrong. The link has opened up a channel to a hacker, and because you are an Administrator, they too can download software to your computer. Be assured that the software they put on your device is not there to help you – it’s there to get your data and to steal funds.
I can provide numerous references of businesses who have fallen victim to cyberattacks that could have been avoided by the simple measure of removal of Administrative rights for all staff – including directors.
Still think you want Admin rights for your computer? Then don’t take my word for it – take a look at the National Cyber Security Centre website. It’s a standard recommendation. It’s worth noting your organisation will receive an immediate-fail on any Cyber Essentials assessment as well.
As we say to all our customers – please listen to our advice. We’re offering it in your own best interests!
PS – in case you’re wondering – I’m a standard user at Fresh Mango Technologies. Just because I’m the MD I neither want nor need ‘Admin rights’. If I need software to be installed on my computer, I do the same as we ask of our customers – I log a support request ????
Why you should leave your computer switched on
We’re often asked if its best to switch your computer off every day. Our answer is ‘no’, and in this article, we set out why we recommend leaving PCs switched on is the good practice today…
We’re often asked if it’s best to switch your computer off every day. Our answer is ‘no’, and in this article, we set out why we recommend leaving PCs switched on is the good practice today.
Switching a computer off is something of a hangover from the early days of PCs. When desktop computers were first introduced they were power-hungry. Their monitors – which were usually integrated – were huge and consumed a lot of electricity. Similarly, the computers generated a lot of heat and needed power-hungry internal fans to keep them cool.
All of this added up to a big electricity bill, especially for larger companies with lots of staff and computers. So the message was drummed into all computer users – switch off before you go home.
Fast forward to the present day and we have a very different scenario. Monitors are now separate devices to computers, with their own power supplies. Monitor technology is LCD, which means they consume far less power than monitors of old.
The PCs themselves still require fans (unless you have a Mac or tablet) but the miniaturisation of components means the power-demand of cooling fans has also decreased.
So all this means that concerns over power-consumption have been largely alleviated. Of course, there is still some power consumption, so why do we recommend leaving PCs switched on? Isn’t there a cybersecurity issue to consider as well?
These are all good points, here is the rationale for leaving your PC switched on when you leave the office (or kitchen table if working from home) for the day:
- It ensures your IT team can conduct updates, health-checks, anti-virus scans and other remote work out-of-hours. This minimises disruption to your business during working hours
- It allows your IT team to conduct emergency security patching out-of-hours in the event of a cyber-attack – an increasingly regular occurrence
- It prolongs the life of your equipment. Turning your PC on and off every day shortens its life.
- As for your electricity bill, your IT team should ensure all displays (the biggest drain on electricity) automatically go to sleep after a few minutes.
So far as cybersecurity is concerned, your IT team should ensure that your login credentials are ‘standard user’ only – ie non-Administrative. So, anyone who successfully hacks your login account remotely won’t get very far – a Standard User has very limited rights for this very reason.
So there you have it – the rationale for leaving your PC switched on! By the way, if your current IT team don’t have your PCs set up as described above, it may be worth getting in touch with the IT professionals at Fresh Mango Technologies!