The Top 5 Phishing Techniques Targeting Staff This Year
And how Fresh Mango Technologies helps you stay one step ahead
Why Phishing Attacks Are Increasing in the Workplace
Phishing attacks remain the number one cause of cyber security breaches, and this year attackers are more sophisticated than ever. While organisations continue to invest in firewalls, email filtering, and endpoint protection, cyber criminals are increasingly focusing on the easiest target: people.
At Fresh Mango Technologies, we work with UK organisations every day and see first‑hand how phishing techniques are evolving. Below are the top five phishing methods targeting staff this year—and how the right training and awareness can stop them.
The Top 5 Phishing Techniques Targeting Staff in 2026
1. AI‑Powered Spear Phishing
Attackers are now using AI to generate highly convincing emails that reference real projects, colleagues, or suppliers. These messages are well written, professional, and often completely free of spelling or grammar mistakes.
Why it works: Staff are used to spotting obvious errors, but AI‑generated emails remove those traditional warning signs.
How Fresh Mango helps: Our Cyber Awareness Training focuses on recognising suspicious behaviour and context, not just poor wording.
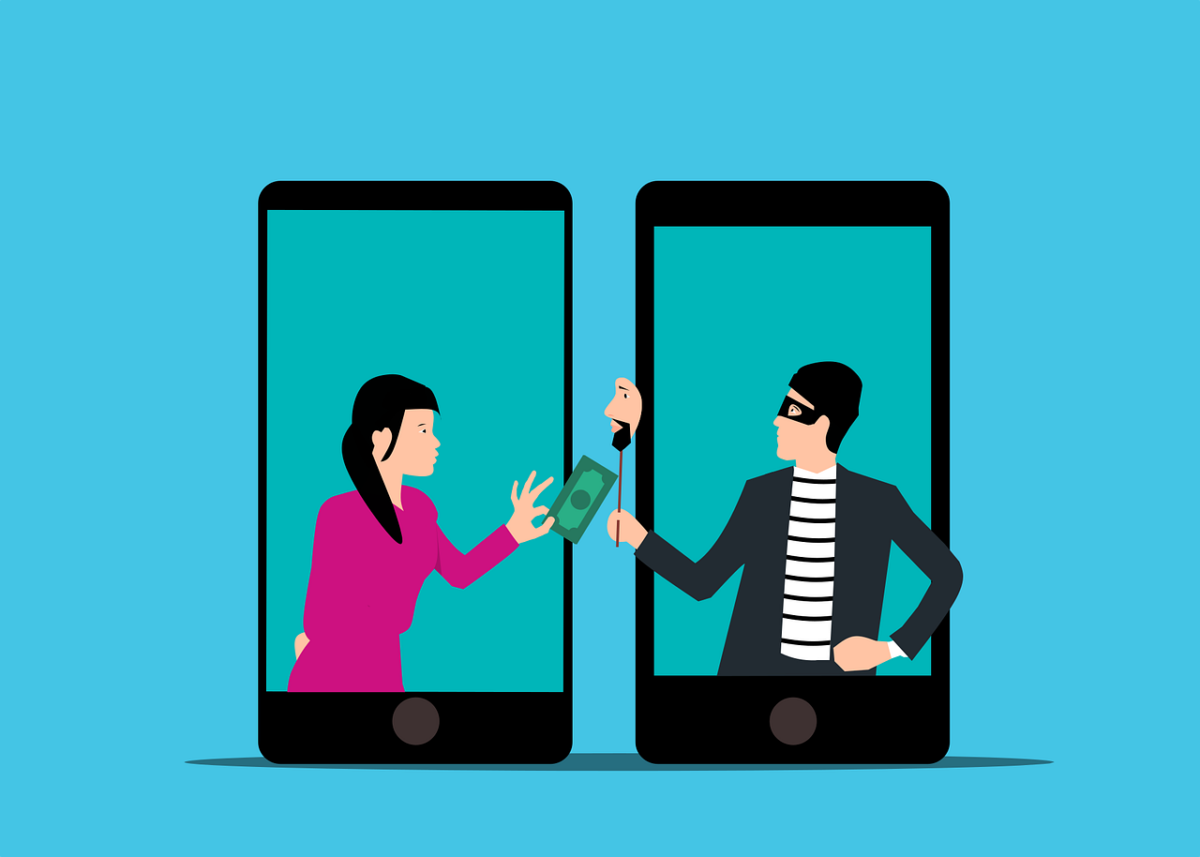
2. Business Email Compromise (BEC) Attacks
BEC attacks impersonate senior leaders or finance teams, requesting urgent payments, bank detail changes, or sensitive information—often late in the day or before weekends.
Why it works: Urgency and authority pressure staff into acting quickly without verification.
How Fresh Mango helps: We train staff to pause, verify, and challenge unusual requests using realistic scenarios delivered through CyberShield.
3. MFA Fatigue Attacks and Push Notification Attacks
Instead of stealing passwords, attackers bombard users with repeated MFA push notifications until someone eventually clicks “Approve” just to stop the alerts.
Why it works: Users assume the prompts are system errors or routine login requests.
How Fresh Mango helps: Our training explains exactly when MFA requests are suspicious and what staff should do instead.
4. QR Code Phishing (Quishing) Attacks
QR codes embedded in emails, invoices, or posters redirect users to fake login pages designed to harvest credentials.
Why it works: QR codes bypass traditional email scanning and feel convenient and trustworthy.
How Fresh Mango helps: We highlight mobile‑based threats that many organisations forget to address.
5. Cloud App and OAuth Consent Phishing
Attackers trick users into granting permissions to malicious apps within Microsoft 365 or Google Workspace, giving attackers long‑term access without stealing passwords.
Why it works: No credentials are entered, so users don’t realise anything is wrong.
How Fresh Mango helps: We teach staff how to identify legitimate consent requests and spot abuse.
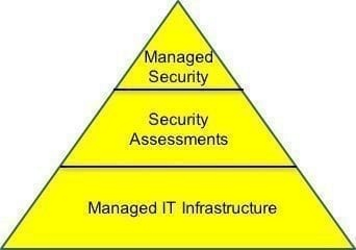
Building a Human Firewall with Fresh Mango Technologies
Technology alone cannot stop phishing. The strongest defence is a well‑trained and regularly reminded workforce.
Fresh Mango Technologies supports organisations with:
- Cyber Awareness Training that is practical, engaging, and written in plain English
- CyberShield, our monthly phishing and security awareness email subscription
- Real‑world attack scenarios based on current threats, not outdated examples
Phishing attacks will continue to evolve—but with the right training and reinforcement, your staff become your strongest line of defence.
If you want to reduce risk, improve resilience, and stop phishing attacks before they succeed, Fresh Mango Technologies is here to help.
Because cyber security isn’t just about systems—it’s about people.